Last week, the United States joined the U.K. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev as the leader of the infamous LockBit ransomware group. LockBit’s leader “LockBitSupp” claims the feds named the wrong guy, saying the charges don’t explain how they connected him to Khoroshev. This post examines the activities of Khoroshev’s many alter egos on the cybercrime forums, and tracks the career of a gifted malware author who has written and sold malicious code for the past 14 years.

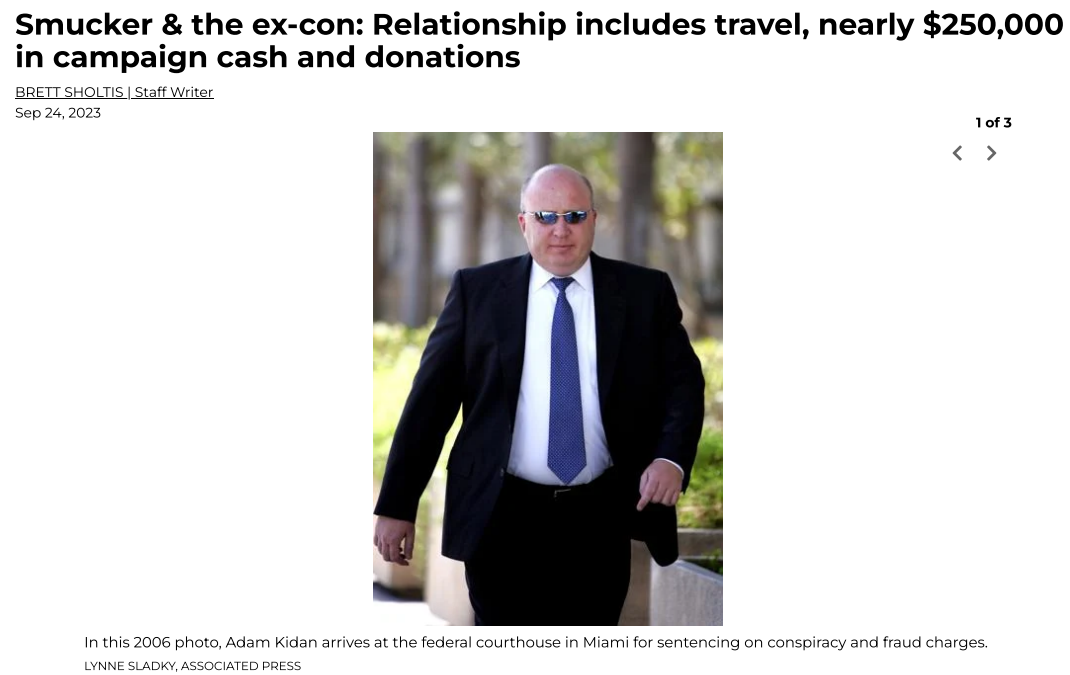
Dmitry Yuryevich Khoroshev. Image: treasury.gov.
On May 7, the U.S. Department of Justice indicted Khoroshev on 26 criminal counts, including extortion, wire fraud, and conspiracy. The government alleges Khoroshev created, sold and used the LockBit ransomware strain to personally extort more than $100 million from hundreds of victim organizations, and that LockBit as a group extorted roughly half a billion dollars over four years.
Federal investigators say Khoroshev ran LockBit as a “ransomware-as-a-service” operation, wherein he kept 20 percent of any ransom amount paid by a victim organization infected with his code, with the remaining 80 percent of the payment going to LockBit affiliates responsible for spreading the malware.
Financial sanctions levied against Khoroshev by the U.S. Department of the Treasury listed his known email and street address (in Voronezh, in southwest Russia), passport number, and even his tax ID number (hello, Russian tax authorities). The Treasury filing says Khoroshev used the emails sitedev5@yandex.ru, and khoroshev1@icloud.com.
According to DomainTools.com, the address sitedev5@yandex.ru was used to register at least six domains, including a Russian business registered in Khoroshev’s name called tkaner.com, which is a blog about clothing and fabrics.
A search at the breach-tracking service Constella Intelligence on the phone number in Tkaner’s registration records — 7.9521020220 — brings up multiple official Russian government documents listing the number’s owner as Dmitri Yurievich Khoroshev.
Another domain registered to that phone number was stairwell[.]ru, which at one point advertised the sale of wooden staircases. Constella finds that the email addresses webmaster@stairwell.ru and admin@stairwell.ru used the password 225948.
DomainTools reports that stairwell.ru for several years included the registrant’s name as “Dmitrij Ju Horoshev,” and the email address pin@darktower.su. According to Constella, this email address was used in 2010 to register an account for a Dmitry Yurievich Khoroshev from Voronezh, Russia at the hosting provider firstvds.ru.

Image: Shutterstock.
Cyber intelligence firm Intel 471 finds that pin@darktower.ru was used by a Russian-speaking member called Pin on the English-language cybercrime forum Opensc. Pin was active on Opensc around March 2012, and authored 13 posts that mostly concerned data encryption issues, or how to fix bugs in code.
Other posts concerned custom code Pin claimed to have written that would bypass memory protections on Windows XP and Windows 7 systems, and inject malware into memory space normally allocated to trusted applications on a Windows machine.
Pin also was active at that same time on the Russian-language security forum Antichat, where they told fellow forum members to contact them at the ICQ instant messenger number 669316.
NEROWOLFE
A search on the ICQ number 669316 at Intel 471 shows that in April 2011, a user by the name NeroWolfe joined the Russian cybercrime forum Zloy using the email address d.horoshev@gmail.com, and from an Internet address in Voronezh, RU.
Constella finds the same password tied to webmaster@stairwell.ru (225948) was used by the email address 3k@xakep.ru, which Intel 471 says was registered to more than a dozen NeroWolfe accounts across just as many Russian cybercrime forums between 2011 and 2015.
NeroWolfe’s introductory post to the forum Verified in Oct. 2011 said he was a system administrator and C++ coder.
“Installing SpyEYE, ZeuS, any DDoS and spam admin panels,” NeroWolfe wrote. This user said they specialize in developing malware, creating computer worms, and crafting new ways to hijack Web browsers.

“I can provide my portfolio on request,” NeroWolfe wrote. “P.S. I don’t modify someone else’s code or work with someone else’s frameworks.”
In April 2013, NeroWolfe wrote in a private message to another Verified forum user that he was selling a malware “loader” program that could bypass all of the security protections on Windows XP and Windows 7.
“The access to the network is slightly restricted,” NeroWolfe said of the loader, which he was selling for $5,000. “You won’t manage to bind a port. However, it’s quite possible to send data. The code is written in C.”
In an October 2013 discussion on the cybercrime forum Exploit, NeroWolfe weighed in on the karmic ramifications of ransomware. At the time, ransomware-as-a-service didn’t exist yet, and many members of Exploit were still making good money from “lockers,” relatively crude programs that locked the user out of their system until they agreed to make a small payment (usually a few hundred dollars via prepaid Green Dot cards).
Lockers, which presaged the coming ransomware scourge, were generally viewed by the Russian-speaking cybercrime forums as harmless moneymaking opportunities, because they usually didn’t seek to harm the host computer or endanger files on the system. Also, there were still plenty of locker programs that aspiring cybercriminals could either buy or rent to make a steady income.
NeroWolfe reminded forum denizens that they were just as vulnerable to ransomware attacks as their would-be victims, and that what goes around comes around.
“Guys, do you have a conscience?,” NeroWolfe wrote. “Okay, lockers, network gopstop aka business in Russian. The last thing was always squeezed out of the suckers. But encoders, no one is protected from them, including the local audience.”
If Khoroshev was ever worried that someone outside of Russia might be able to connect his early hacker handles to his real life persona, that’s not clear from reviewing his history online. In fact, the same email address tied to so many of NeroWolfe’s accounts on the forums — 3k@xakep.ru — was used in 2011 to create an account for a Dmitry Yurevich Khoroshev on the Russian social media network Vkontakte.
NeroWolfe seems to have abandoned all of his forum accounts sometime in 2016. In November 2016, an exploit[.]ru member filed an official complaint against NeroWolfe, saying NeroWolfe had been paid $2,000 to produce custom code but never finished the project and vanished.
It’s unclear what happened to NeroWolfe or to Khoroshev during this time. Maybe he got arrested, or some close associates did. Perhaps he just decided it was time to lay low and hit the reset on his operational security efforts, given his past failures in this regard. It’s also possible NeroWolfe landed a real job somewhere for a few years, fathered a child, and/or had to put his cybercrime career on hold.
PUTINKRAB
Or perhaps Khoroshev saw the coming ransomware industry for the endless pot of gold that it was about to become, and then dedicated himself to working on custom ransomware code. That’s what the government believes.
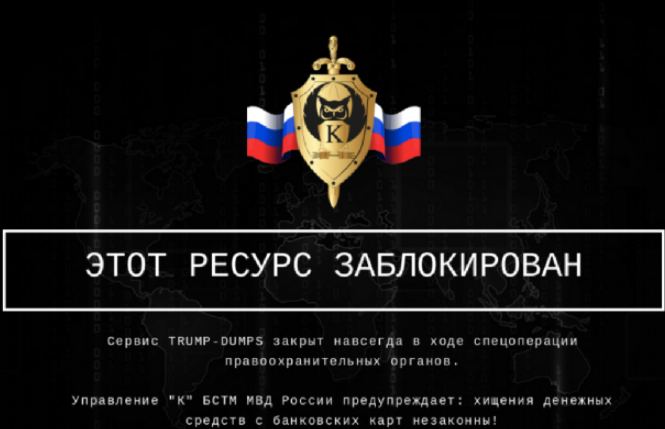
The indictment against Khoroshev says he used the hacker nickname Putinkrab, and Intel 471 says this corresponds to a username that was first registered across three major Russian cybercrime forums in early 2019.
KrebsOnSecurity could find no obvious connections between Putinkrab and any of Khoroshev’s older identities. However, if Putinkrab was Khoroshev, he would have learned from his past mistakes and started fresh with a new identity (which he did). But also, it is likely the government hasn’t shared all of the intelligence it has collected against him (more on that in a bit).
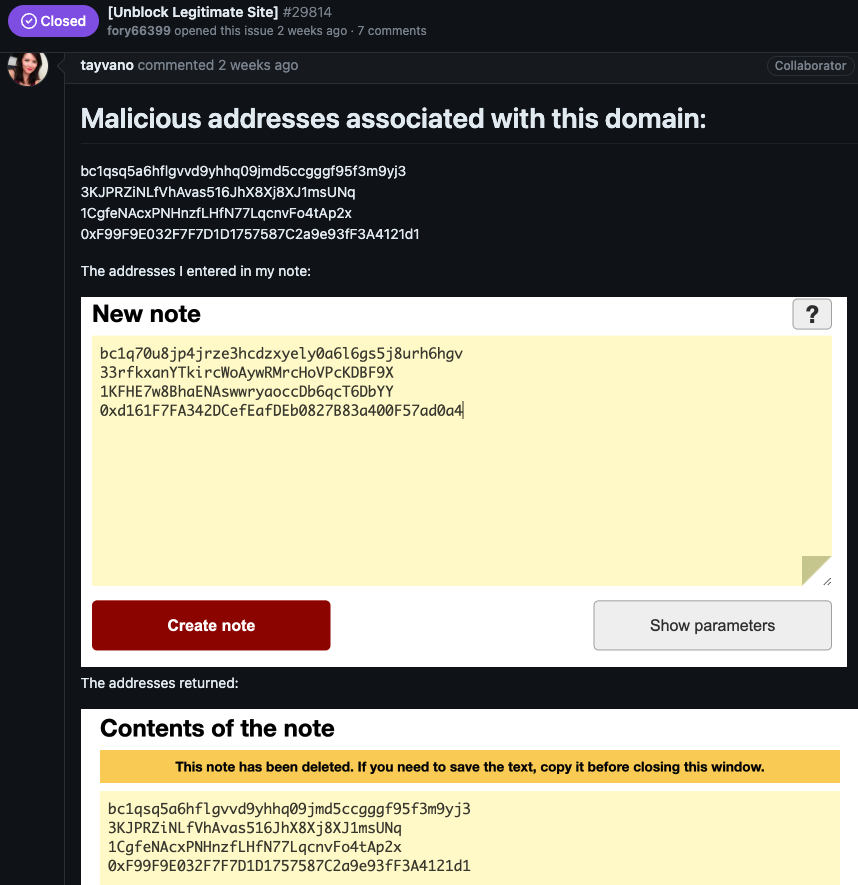
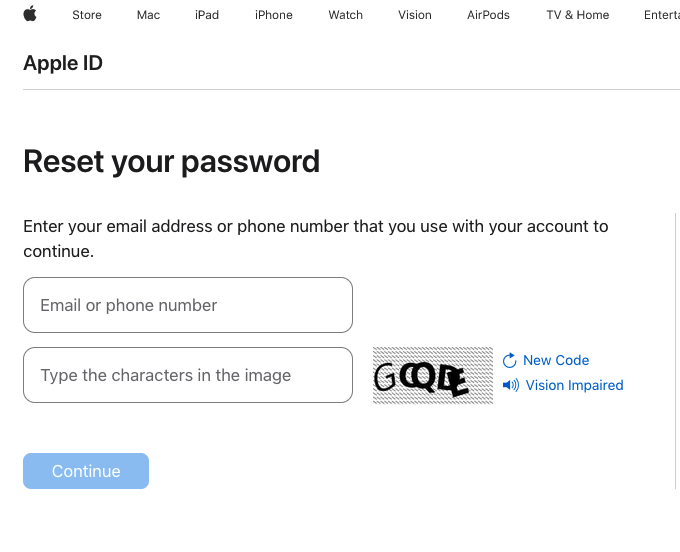
Putinkrab’s first posts on the Russian cybercrime forums XSS, Exploit and UFOLabs saw this user selling ransomware source code written in C.
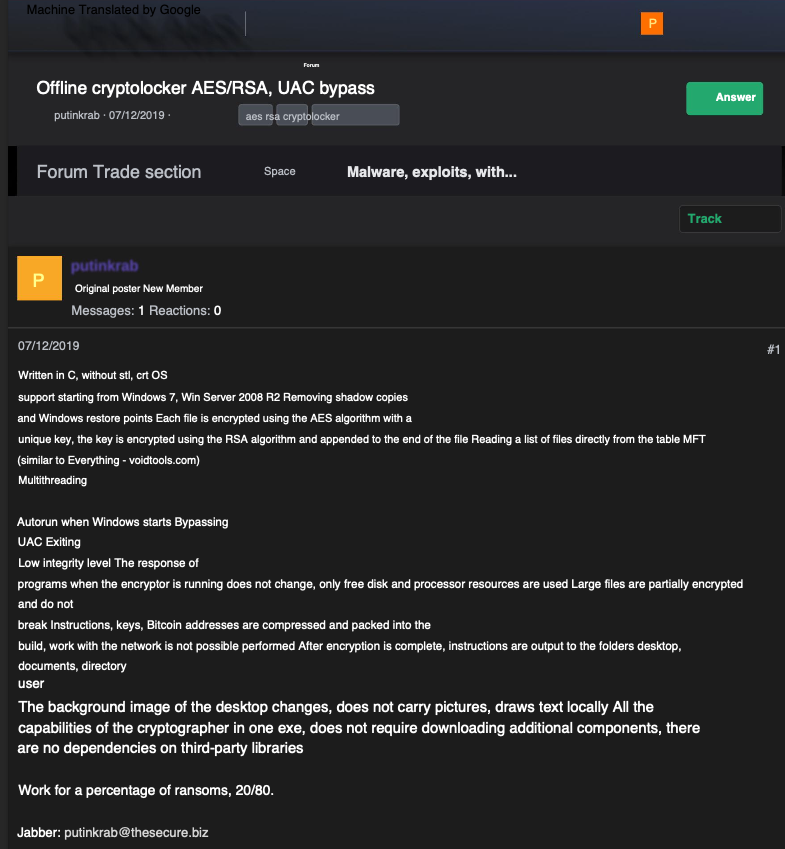
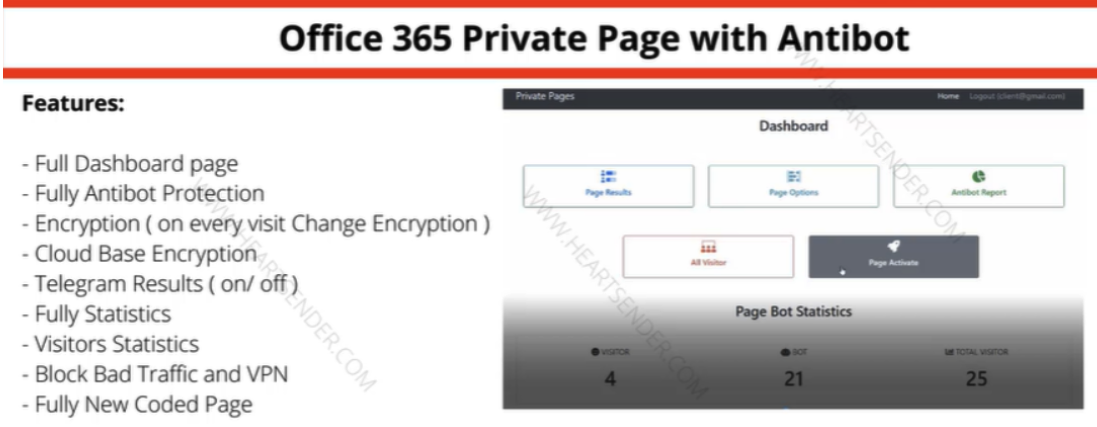
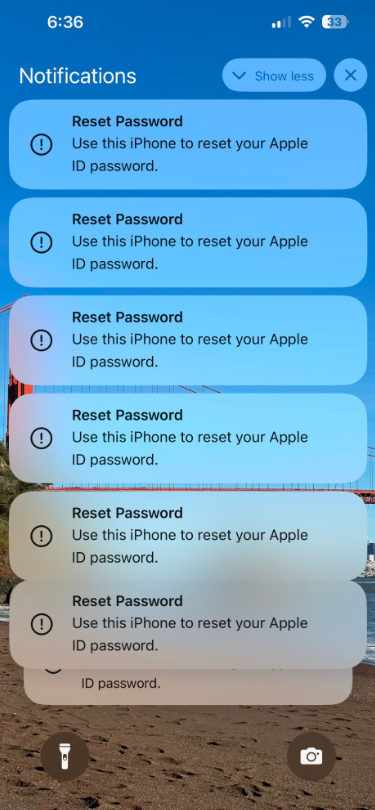
A machine-translated ad for ransomware source code from Putinkrab on the Russian language cybercrime forum UFOlabs in 2019. Image: Ke-la.com.
In April 2019, Putkinkrab offered an affiliate program that would run on top of his custom-made ransomware code.
“I want to work for a share of the ransoms: 20/80,” Putinkrab wrote on Exploit. “20 percent is my percentage for the work, you get 80% of the ransoms. The percentage can be reduced up to 10/90 if the volumes are good. But now, temporarily, until the service is fully automated, we are working using a different algorithm.”
Throughout the summer of 2019, Putinkrab posted multiple updates to Exploit about new features being added to his ransomware strain, as well as novel evasion techniques to avoid detection by security tools. He also told forum members he was looking for investors for a new ransomware project based on his code.
In response to an Exploit member who complained that the security industry was making it harder to profit from ransomware, Putinkrab said that was because so many cybercriminals were relying on crappy ransomware code.
“The vast majority of top antiviruses have acquired behavioral analysis, which blocks 95% of crypto-lockers at their root,” Putinkrab wrote. “Cryptolockers made a lot of noise in the press, but lazy system administrators don’t make backups after that. The vast majority of cryptolockers are written by people who have little understanding of cryptography. Therefore, decryptors appear on the Internet, and with them the hope that files can be decrypted without paying a ransom. They just sit and wait. Contact with the owner of the key is lost over time.”
Putinkrab said he had every confidence his ransomware code was a game-changer, and a huge money machine.
“The game is just gaining momentum,” Putinkrab wrote. “Weak players lose and are eliminated.”
The rest of his response was structured like a poem:
“In this world, the strongest survive.
Our life is just a struggle.
The winner will be the smartest,
Who has his head on his shoulders.”
Putinkrab’s final post came on August 23, 2019. The Justice Department says the LockBit ransomware affiliate program was officially launched five months later. From there on out, the government says, Khoroshev adopted the persona of LockBitSupp. In his introductory post on Exploit, LockBit’s mastermind said the ransomware strain had been in development since September 2019.
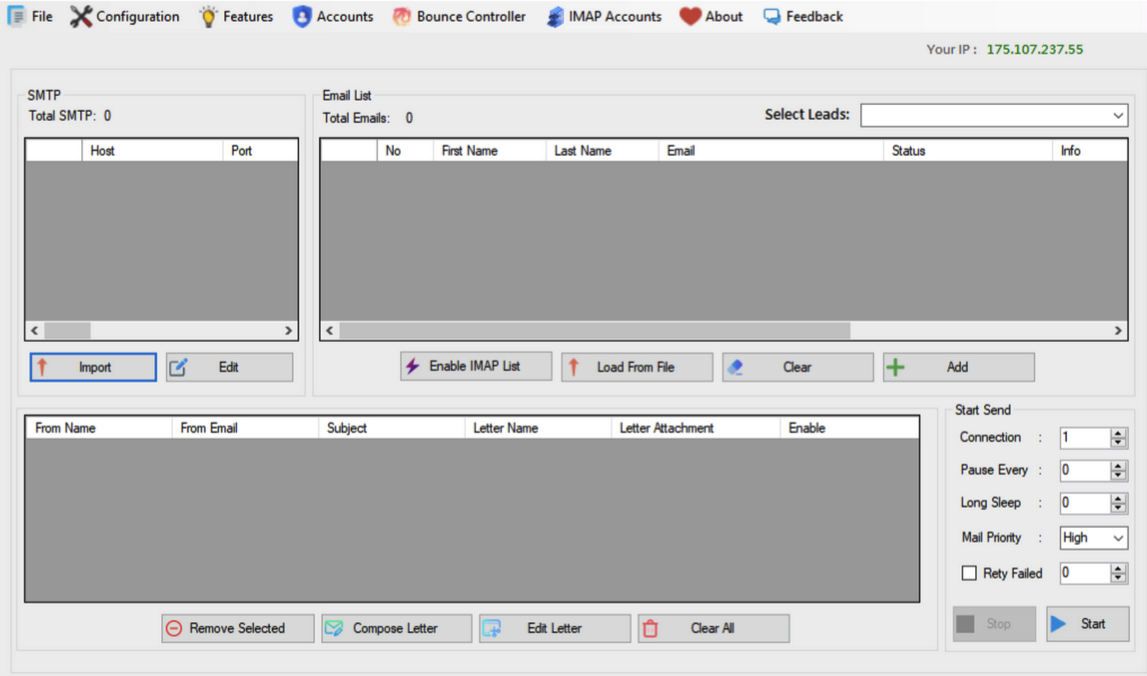
The original LockBit malware was written in C (a language that NeroWolfe excelled at). Here’s the original description of LockBit, from its maker:
“The software is written in C and Assembler; encryption is performed through the I/O Completion Port; there is a port scanning local networks and an option to find all DFS, SMB, WebDAV network shares, an admin panel in Tor, automatic test decryption; a decryption tool is provided; there is a chat with Push notifications, a Jabber bot that forwards correspondence and an option to terminate services/processes in line which prevent the ransomware from opening files at a certain moment. The ransomware sets file permissions and removes blocking attributes, deletes shadow copies, clears logs and mounts hidden partitions; there is an option to drag-and-drop files/folders and a console/hidden mode. The ransomware encrypts files in parts in various places: the larger the file size, the more parts there are. The algorithms used are AES + RSA.
You are the one who determines the ransom amount after communicating with the victim. The ransom paid in any currency that suits you will be transferred to your wallets. The Jabber bot serves as an admin panel and is used for banning, providing decryption tools, chatting – Jabber is used for absolutely everything.”
CONCLUSION
Does the above timeline prove that NeroWolfe/Khoroshev is LockBitSupp? No. However, it does indicate Khoroshev was for many years deeply invested in countless schemes involving botnets, stolen data, and malware he wrote that others used to great effect. NeroWolfe’s many private messages from fellow forum members confirm this.
NeroWolfe’s specialty was creating custom code that employed novel stealth and evasion techniques, and he was always quick to volunteer his services on the forums whenever anyone was looking help on a malware project that called for a strong C or C++ programmer.
Someone with those qualifications — as well as demonstrated mastery of data encryption and decryption techniques — would have been in great demand by the ransomware-as-a-service industry that took off at around the same time NeroWolfe vanished from the forums.
Someone like that who is near or at the top of their game vis-a-vis their peers does not simply walk away from that level of influence, community status, and potential income stream unless forced to do so by circumstances beyond their immediate control.
It’s important to note that Putinkrab didn’t just materialize out of thin air in 2019 — suddenly endowed with knowledge about how to write advanced, stealthy ransomware strains. That knowledge clearly came from someone who’d already had years of experience building and deploying ransomware strains against real-life victim organizations.
Thus, whoever Putinkrab was before they adopted that moniker, it’s a safe bet they were involved in the development and use of earlier, highly successful ransomware strains. One strong possible candidate is Cerber ransomware, the most popular and effective affiliate program operating between early 2016 and mid-2017. Cerber thrived because it emerged as an early mover in the market for ransomware-as-a-service offerings.
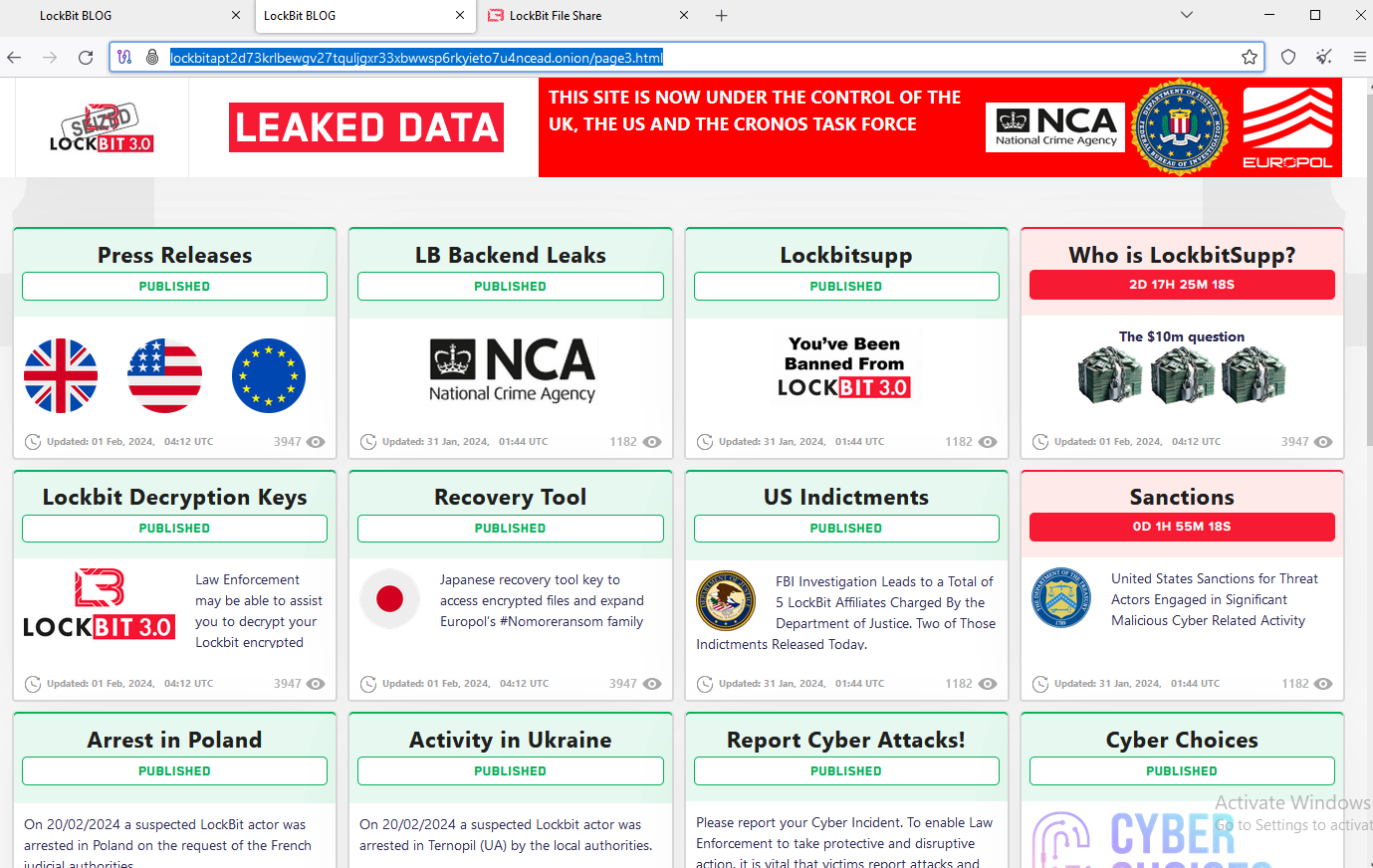
In February 2024, the FBI seized LockBit’s cybercrime infrastructure on the dark web, following an apparently lengthy infiltration of the group’s operations. The United States has already indicted and sanctioned at least five other alleged LockBit ringleaders or affiliates, so presumably the feds have been able to draw additional resources from those investigations.
Also, it seems likely that the three national intelligence agencies involved in bringing these charges are not showing all of their cards. For example, the Treasury documents on Khoroshev mention a single cryptocurrency address, and yet experts interviewed for this story say there are no obvious clues connecting this address to Khoroshev or Putinkrab.
But given that LockBitSupp has been actively involved in Lockbit ransomware attacks against organizations for four years now, the government almost certainly has an extensive list of the LockBit leader’s various cryptocurrency addresses — and probably even his bank accounts in Russia. And no doubt the money trail from some of those transactions was traceable to its ultimate beneficiary (or close enough).
Not long after Khoroshev was charged as the leader of LockBit, a number of open-source intelligence accounts on Telegram began extending the information released by the Treasury Department. Within hours, these sleuths had unearthed more than a dozen credit card accounts used by Khoroshev over the past decade, as well as his various bank account numbers in Russia.
The point is, this post is based on data that’s available to and verifiable by KrebsOnSecurity. Woodward & Bernstein’s source in the Watergate investigation — Deep Throat — famously told the two reporters to “follow the money.” This is always excellent advice. But these days, that can be a lot easier said than done — especially with people who a) do not wish to be found, and b) don’t exactly file annual reports.