The Biden administration today issued its vision for beefing up the nation’s collective cybersecurity posture, including calls for legislation establishing liability for software products and services that are sold with little regard for security. The White House’s new national cybersecurity strategy also envisions a more active role by cloud providers and the U.S. military in disrupting cybercriminal infrastructure, and it names China as the single biggest cyber threat to U.S. interests.

The strategy says the White House will work with Congress and the private sector to develop legislation that would prevent companies from disavowing responsibility for the security of their software products or services.
Coupled with this stick would be a carrot: An as-yet-undefined “safe harbor framework” that would lay out what these companies could do to demonstrate that they are making cybersecurity a central concern of their design and operations.
“Any such legislation should prevent manufacturers and software publishers with market power from fully disclaiming liability by contract, and establish higher standards of care for software in specific high-risk scenarios,” the strategy explains. “To begin to shape standards of care for secure software development, the Administration will drive the development of an adaptable safe harbor framework to shield from liability companies that securely develop and maintain their software products and services.”
Brian Fox, chief technology officer and founder of the software supply chain security firm Sonatype, called the software liability push a landmark moment for the industry.
“Market forces are leading to a race to the bottom in certain industries, while contract law allows software vendors of all kinds to shield themselves from liability,” Fox said. “Regulations for other industries went through a similar transformation, and we saw a positive result — there’s now an expectation of appropriate due care, and accountability for those who fail to comply. Establishing the concept of safe harbors allows the industry to mature incrementally, leveling up security best practices in order to retain a liability shield, versus calling for sweeping reform and unrealistic outcomes as previous regulatory attempts have.”
THE MOST ACTIVE, PERSISTENT THREAT
In 2012 (approximately three national cyber strategies ago), then director of the U.S. National Security Agency (NSA) Keith Alexander made headlines when he remarked that years of successful cyber espionage campaigns from Chinese state-sponsored hackers represented “the greatest transfer of wealth in history.”
The document released today says the People’s Republic of China (PRC) “now presents the broadest, most active, and most persistent threat to both government and private sector networks,” and says China is “the only country with both the intent to reshape the international order and, increasingly, the economic, diplomatic, military, and technological power to do so.”
Many of the U.S. government’s efforts to restrain China’s technology prowess involve ongoing initiatives like the CHIPS Act, a new law signed by President Biden last year that sets aside more than $50 billion to expand U.S.-based semiconductor manufacturing and research and to make the U.S. less dependent on foreign suppliers; the National Artificial Intelligence Initiative; and the National Strategy to Secure 5G.
As the maker of most consumer gizmos with a computer chip inside, China is also the source of an incredible number of low-cost Internet of Things (IoT) devices that are not only poorly secured, but are probably more accurately described as insecure by design.
The Biden administration said it would continue its previously announced plans to develop a system of labeling that could be applied to various IoT products and give consumers some idea of how secure the products may be. But it remains unclear how those labels might apply to products made by companies outside of the United States.
FIGHTING BADNESS IN THE CLOUD
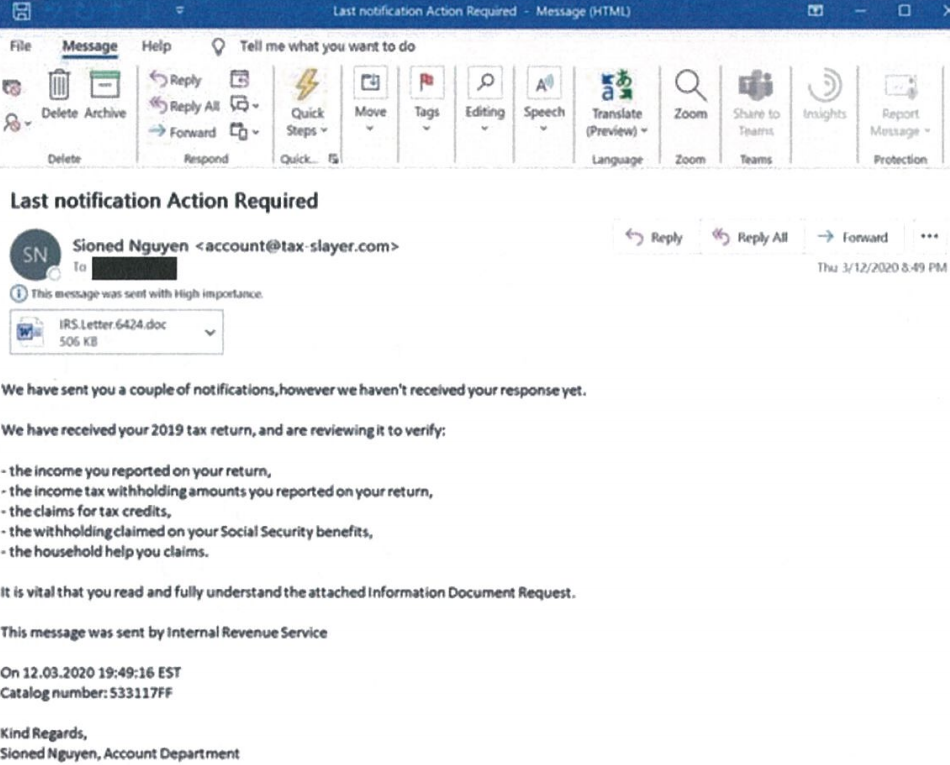
One could convincingly make the case that the world has witnessed yet another historic transfer of wealth and trade secrets over the past decade — in the form of ransomware and data ransom attacks by Russia-based cybercriminal syndicates, as well as Russian intelligence agency operations like the U.S. government-wide Solar Winds compromise.

On the ransomware front, the White House strategy seems to focus heavily on building the capability to disrupt the digital infrastructure used by adversaries that are threatening vital U.S. cyber interests. The document points to the 2021 takedown of the Emotet botnet — a cybercrime machine that was heavily used by multiple Russian ransomware groups — as a model for this activity, but says those disruptive operations need to happen faster and more often.
To that end, the Biden administration says it will expand the capacity of the National Cyber Investigative Joint Task Force (NCIJTF), the primary federal agency for coordinating cyber threat investigations across law enforcement agencies, the intelligence community, and the Department of Defense.
“To increase the volume and speed of these integrated disruption campaigns, the Federal Government must further develop technological and organizational platforms that enable continuous, coordinated operations,” the strategy observes. “The NCIJTF will expand its capacity to coordinate takedown and disruption campaigns with greater speed, scale, and frequency. Similarly, DoD and the Intelligence Community are committed to bringing to bear their full range of complementary authorities to disruption campaigns.”
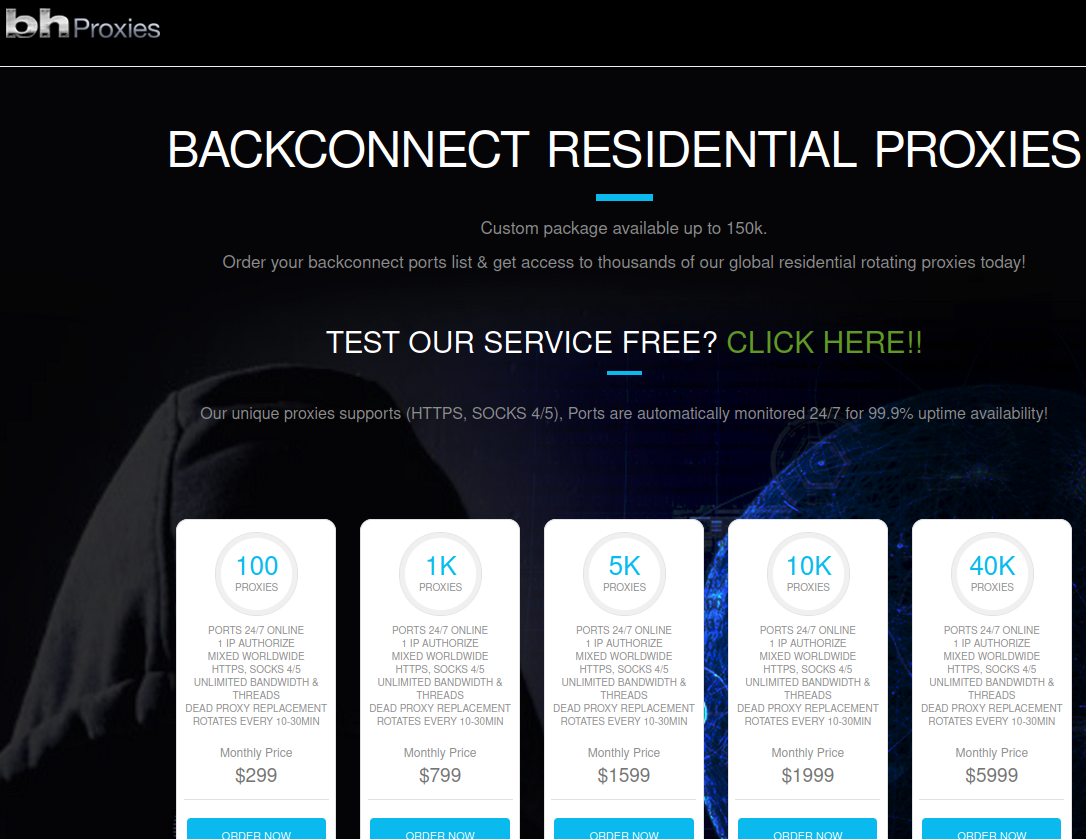
The strategy anticipates the U.S. government working more closely with cloud and other Internet infrastructure providers to quickly identify malicious use of U.S.-based infrastructure, share reports of malicious use with the government, and make it easier for victims to report abuse of these systems.
“Given the interest of the cybersecurity community and digital infrastructure owners and operators in continuing this approach, we must sustain and expand upon this model so that collaborative disruption operations can be carried out on a continuous basis,” the strategy argues. “Threat specific collaboration should take the form of nimble, temporary cells, comprised of a small number of trusted operators, hosted and supported by a relevant hub. Using virtual collaboration platforms, members of the cell would share information bidirectionally and work rapidly to disrupt adversaries.”
But here, again, there is a carrot-and-stick approach: The administration said it is taking steps to implement Executive Order (EO) 13984 –issued by the Trump administration in January 2021 — which requires cloud providers to verify the identity of foreign persons using their services.
“All service providers must make reasonable attempts to secure the use of their infrastructure against abuse or other criminal behavior,” the strategy states. “The Administration will prioritize adoption and enforcement of a risk-based approach to cybersecurity across Infrastructure-as-a-Service providers that addresses known methods and indicators of malicious activity including through implementation of EO 13984.”
Ted Schlein, founding partner of the cybersecurity venture capital firm Ballistic Ventures, said how this gets implemented will determine whether it can be effective.
“Adversaries know the NSA, which is the elite portion of the nation’s cyber defense, cannot monitor U.S.-based infrastructure, so they just use U.S.-based cloud infrastructure to perpetrate their attacks,” Schlein said. “We have to fix this. I believe some of this section is a bit pollyannaish, as it assumes a bad actor with a desire to do a bad thing will self-identify themselves, as the major recommendation here is around KYC (‘know your customer’).”
INSURING THE INSURERS
One brief but interesting section of the strategy titled “Explore a Federal Cyber Insurance Backdrop” contemplates the government’s liability and response to a too-big-to-fail scenario or “catastrophic cyber incident.”
“We will explore how the government can stabilize insurance markets against catastrophic risk to drive better cybersecurity practices and to provide market certainty when catastrophic events do occur,” the strategy reads.
When the Bush administration released the first U.S. national cybersecurity strategy 20 years ago after the 9/11 attacks, the popular term for that same scenario was a “digital Pearl Harbor,” and there was a great deal of talk then about how the cyber insurance market would soon help companies shore up their cybersecurity practices.
In the wake of countless ransomware intrusions, many companies now hold cybersecurity insurance to help cover the considerable costs of responding to such intrusions. Leaving aside the question of whether insurance coverage has helped companies improve security, what happens if every one of these companies has to make a claim at the same time?
The notion of a Digital Pearl Harbor incident struck many experts at the time as a hyperbolic justification for expanding the government’s digital surveillance capabilities, and an overstatement of the capabilities of our adversaries. But back in 2003, most of the world’s companies didn’t host their entire business in the cloud.
Today, nobody questions the capabilities, goals and outcomes of dozens of nation-state level cyber adversaries. And these days, a catastrophic cyber incident could be little more than an extended, simultaneous outage at multiple cloud providers.
The full national cybersecurity strategy is available from the White House website (PDF).